analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
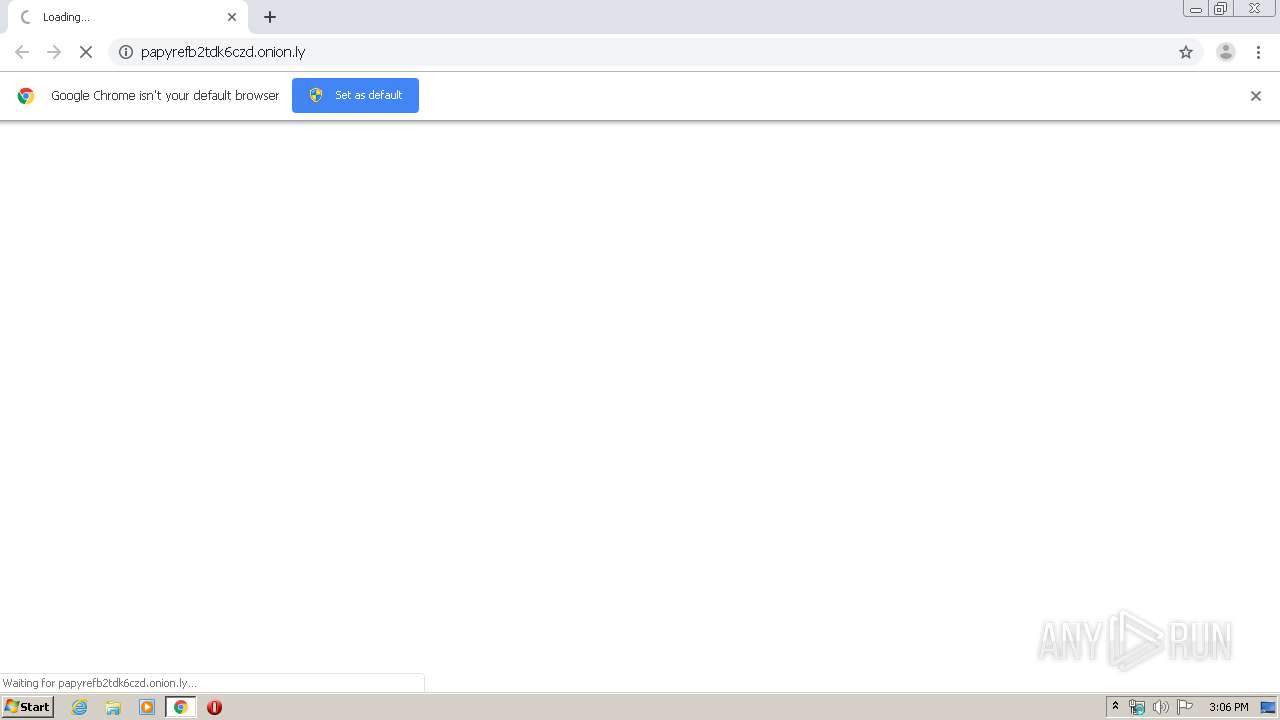
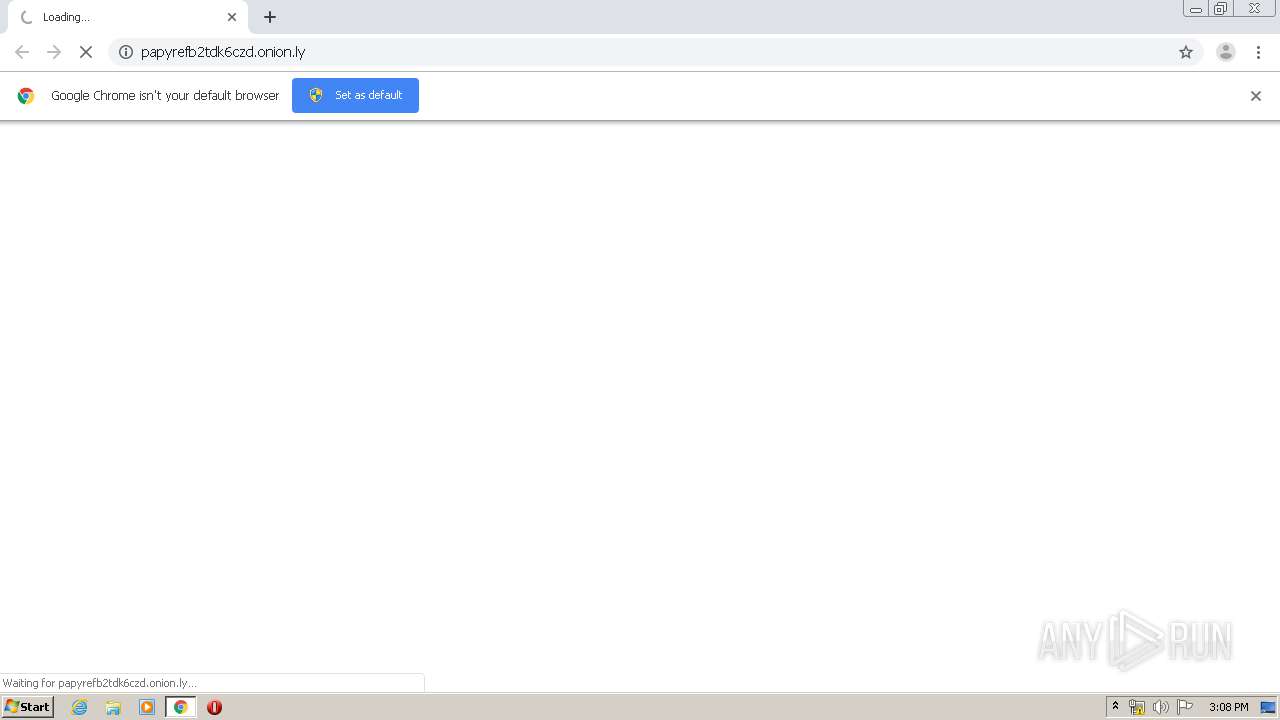
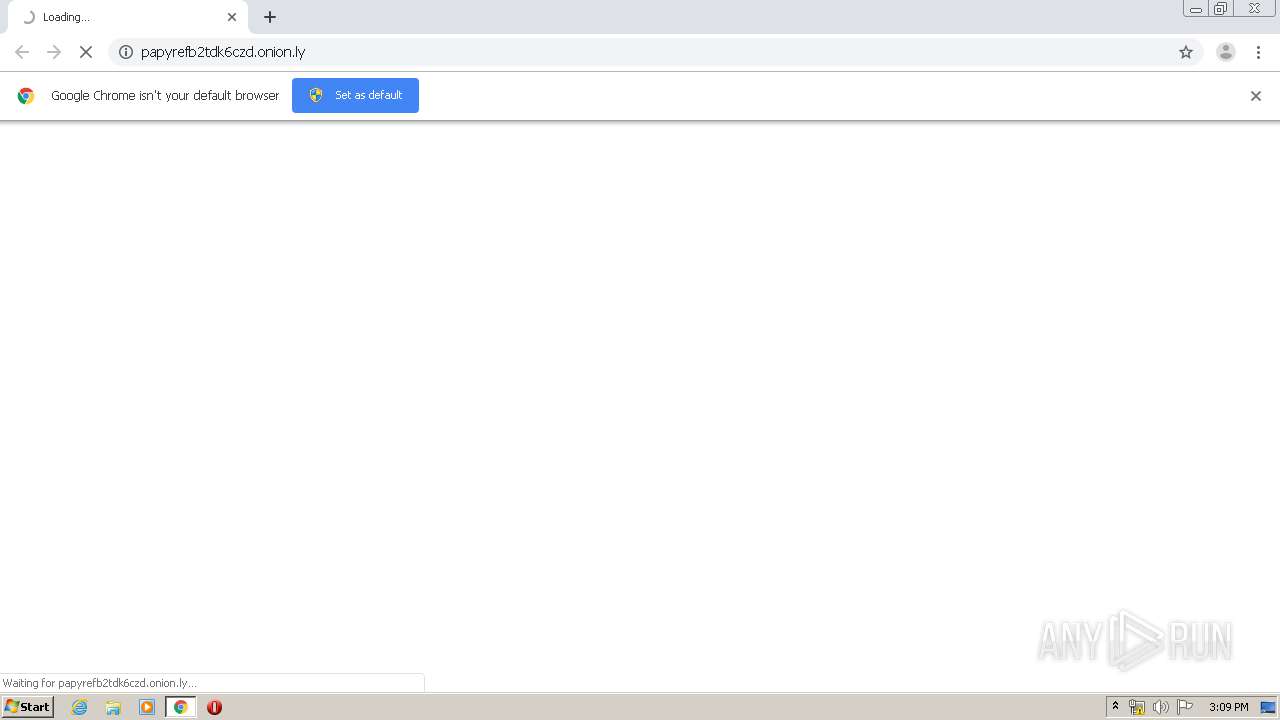
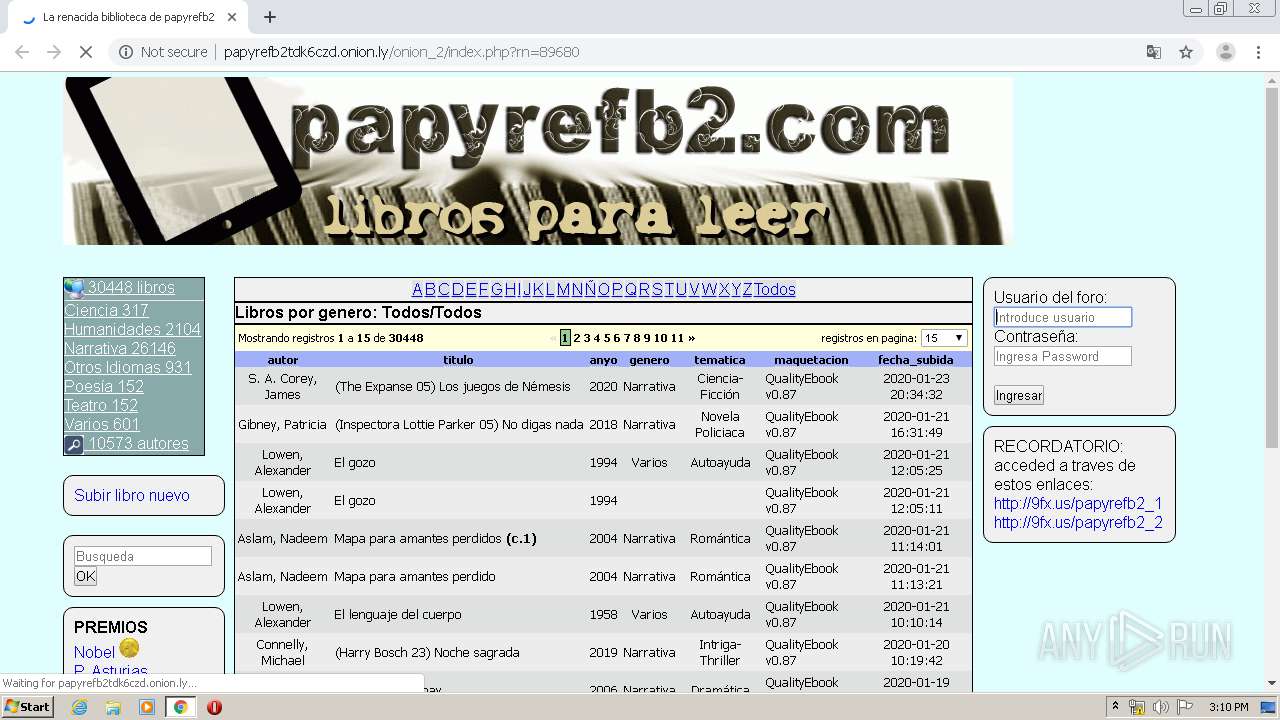
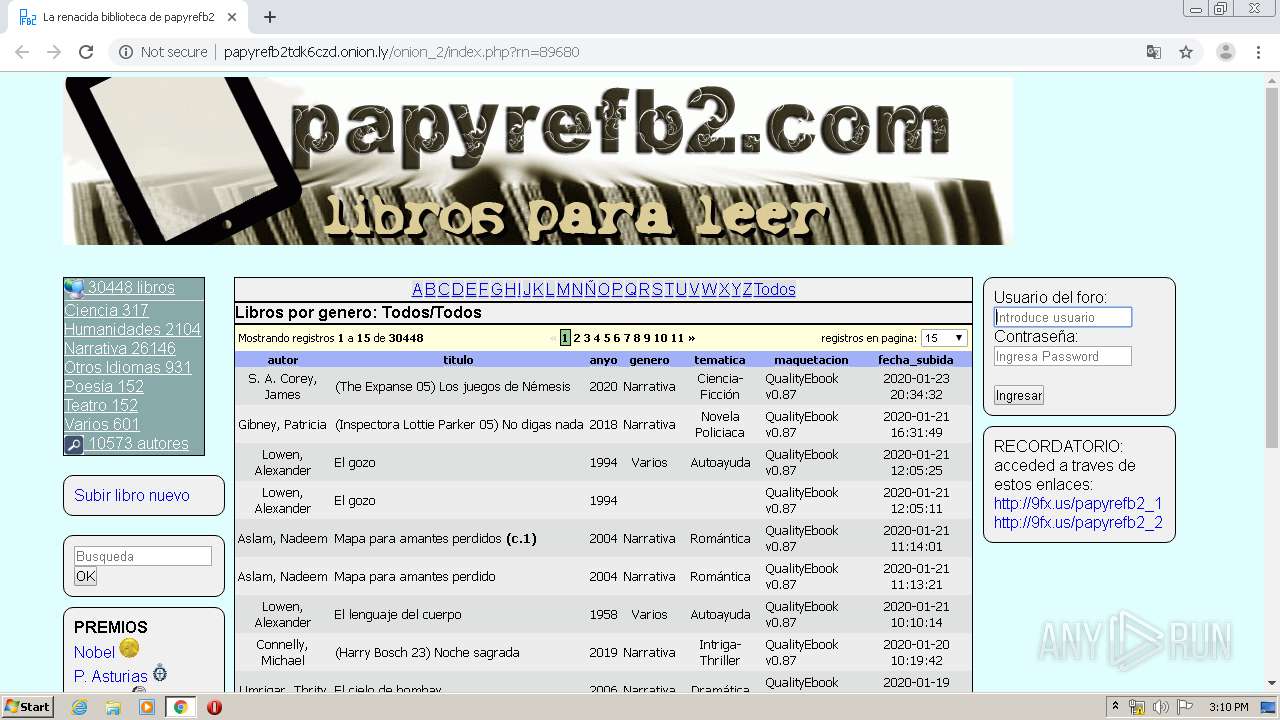
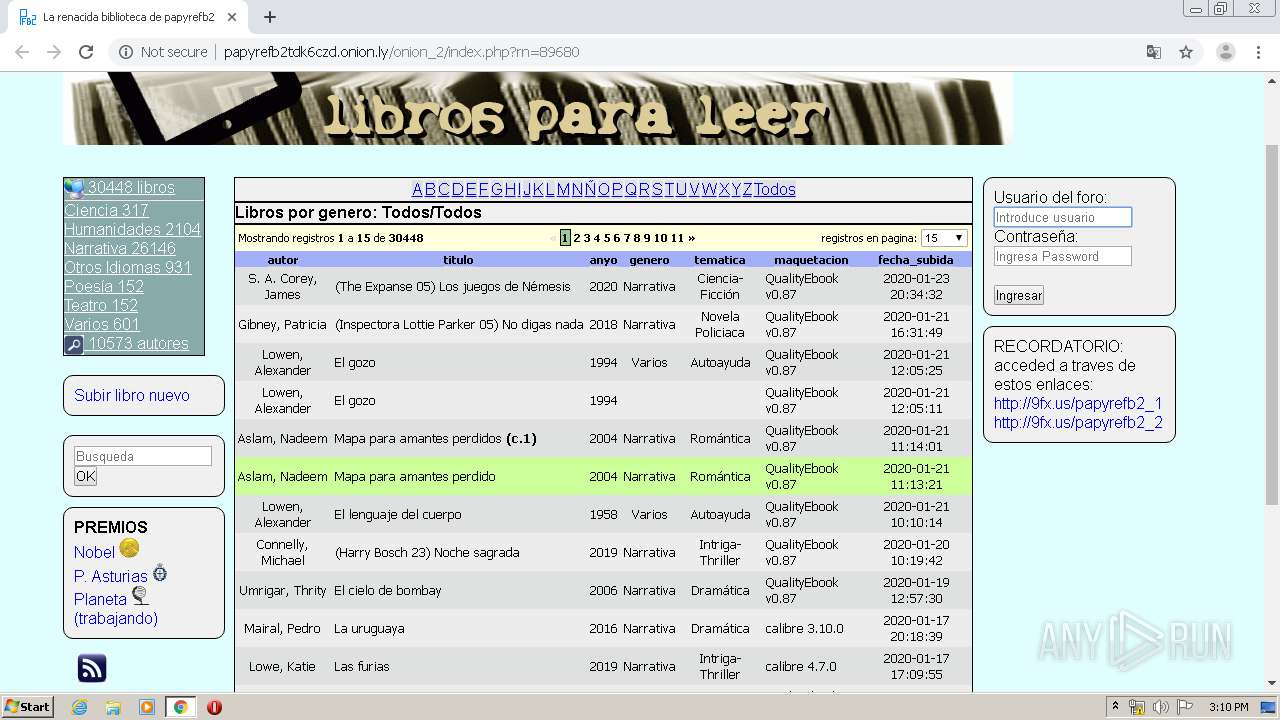
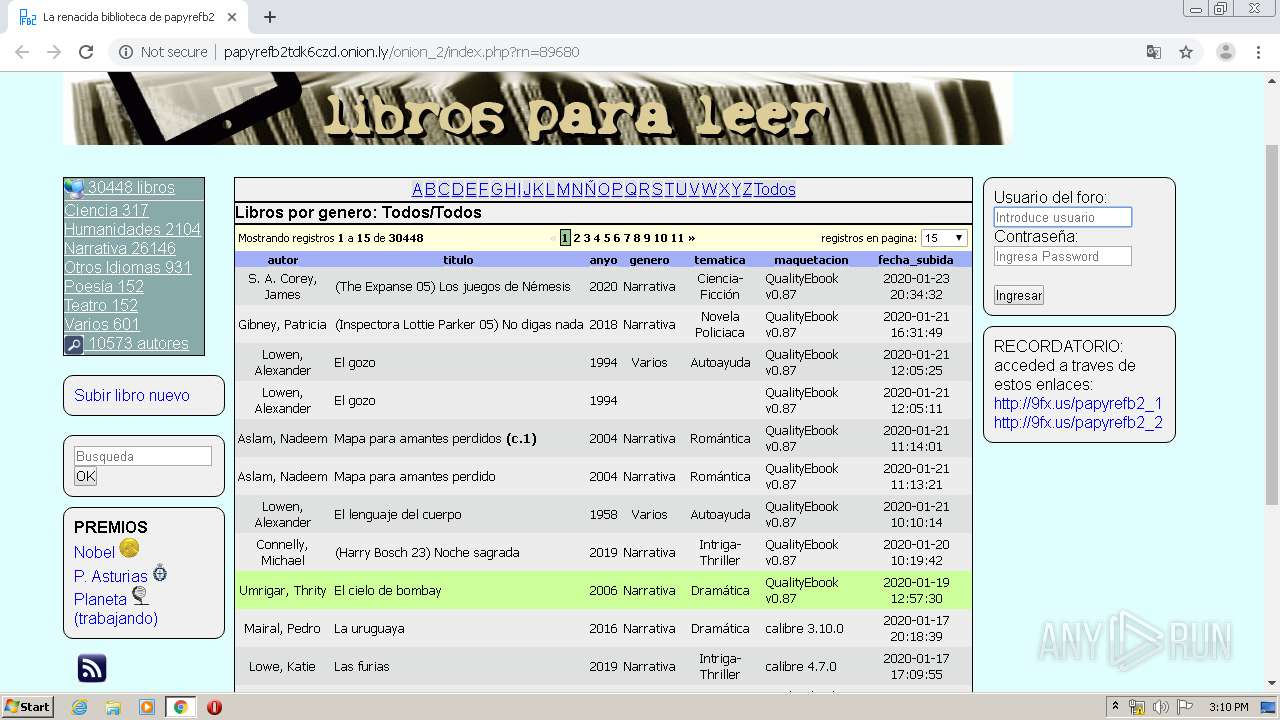
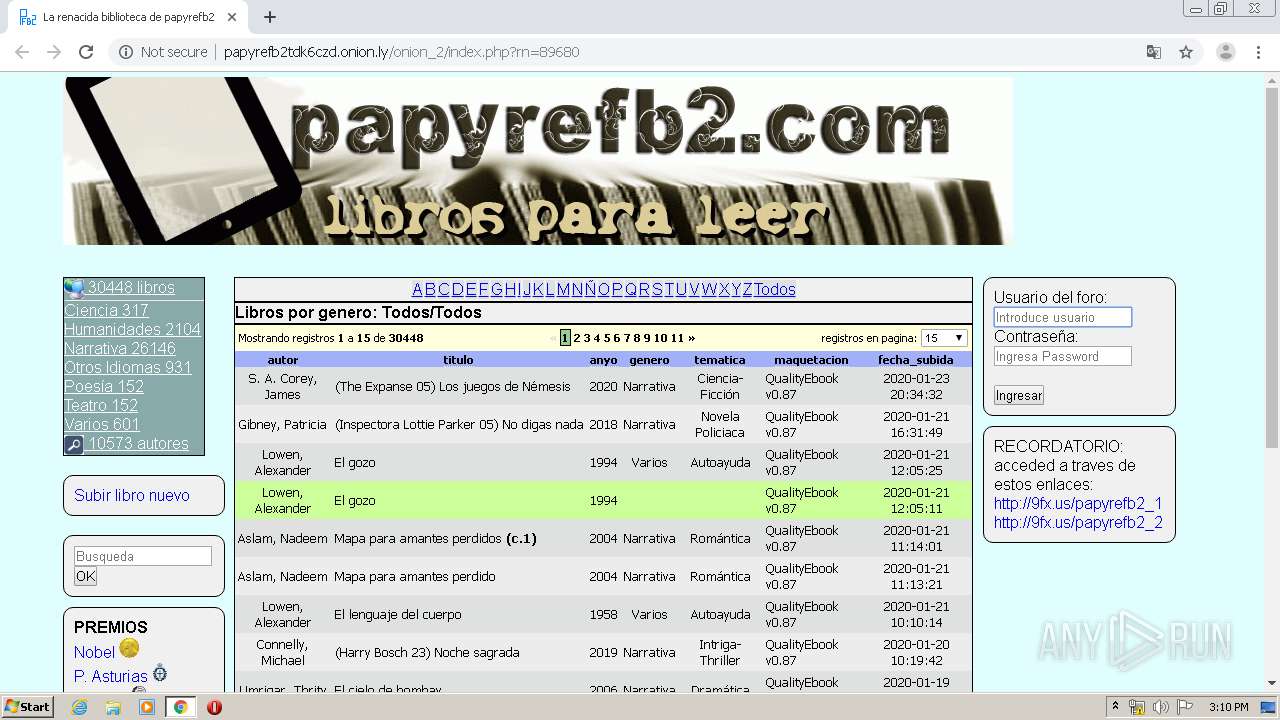
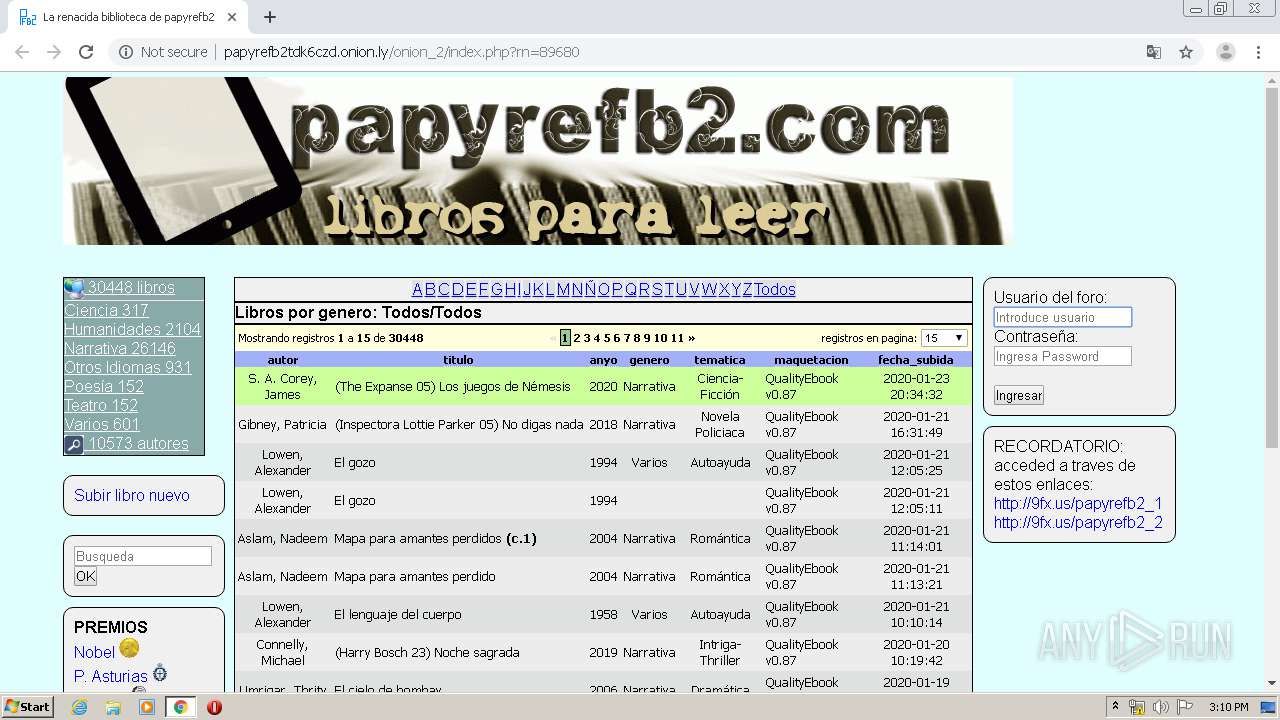
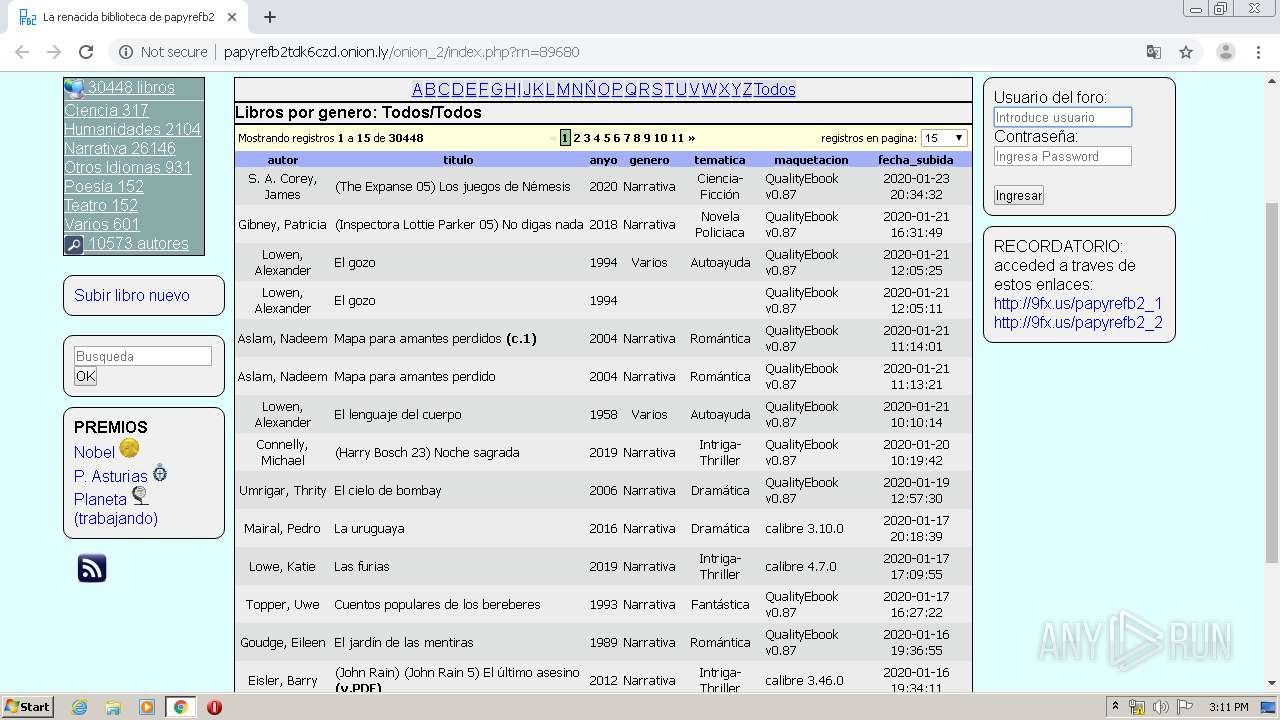
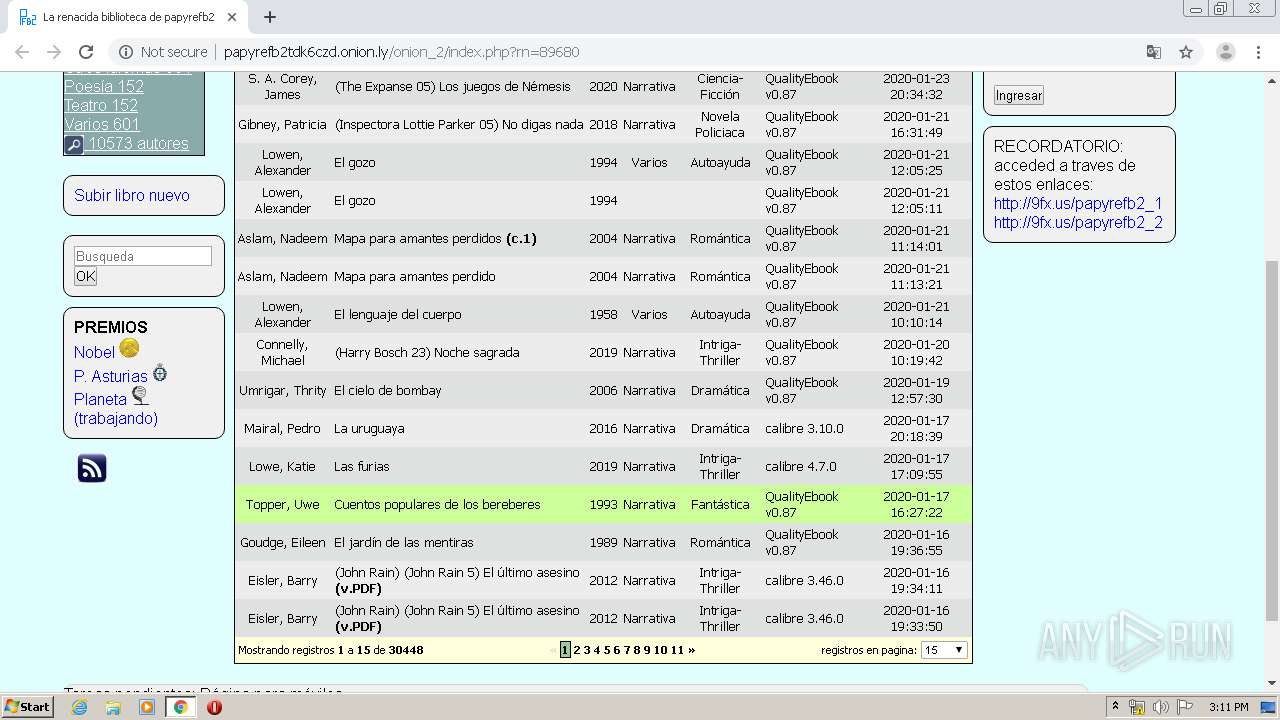
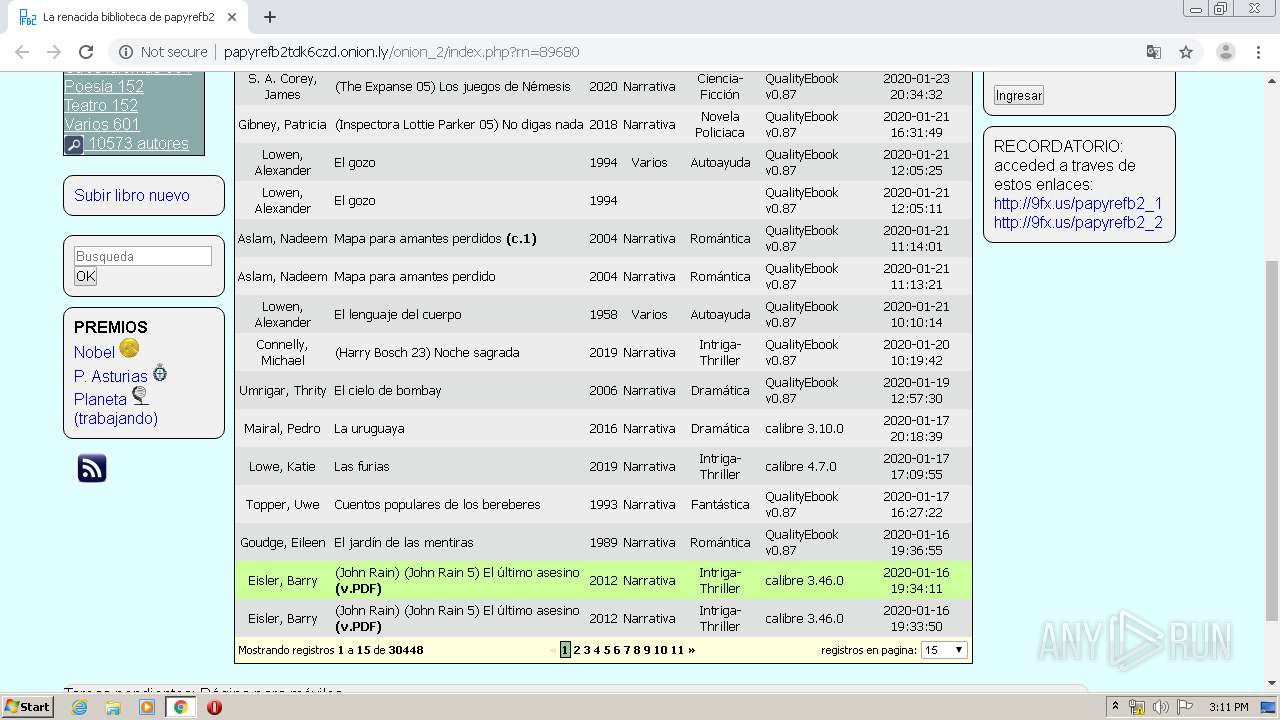
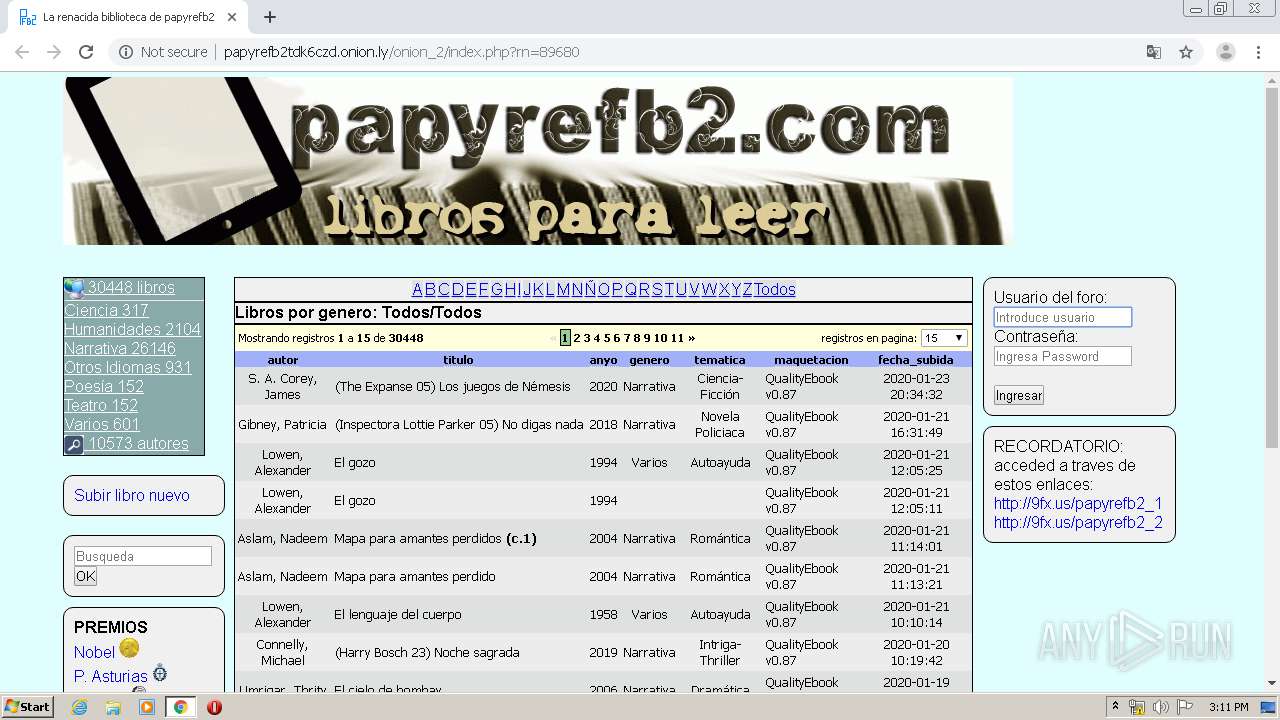
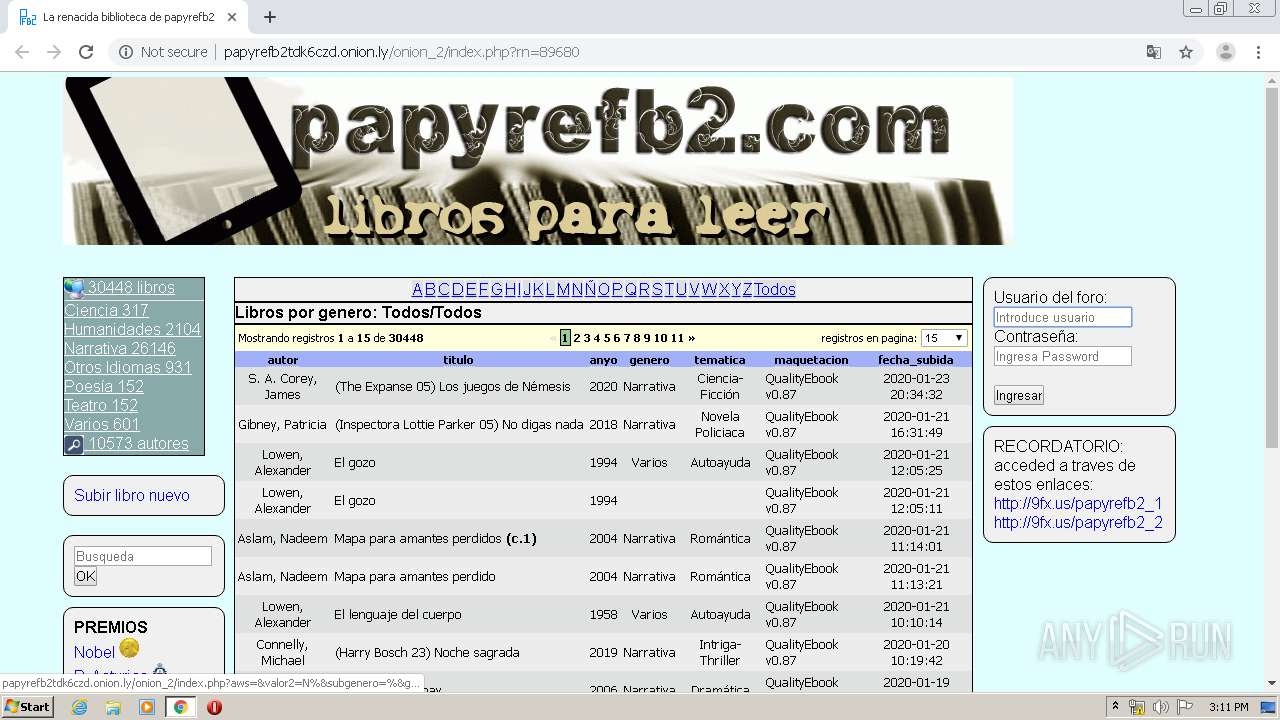
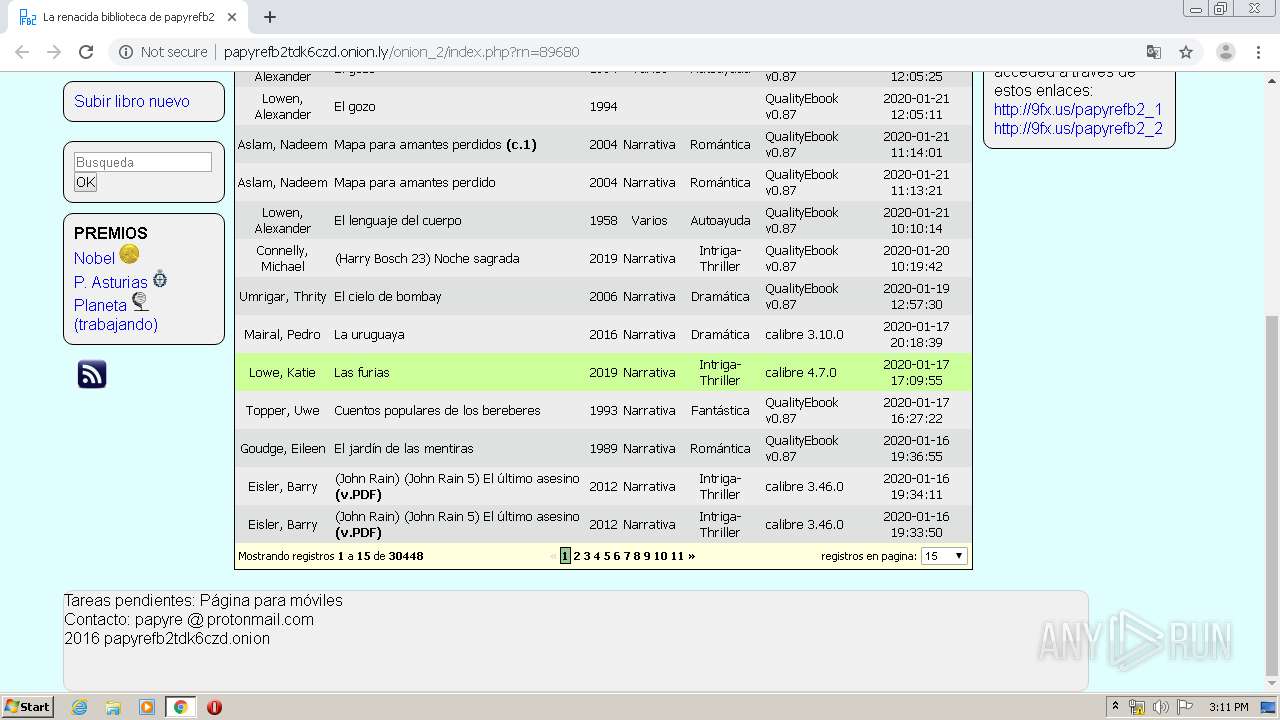
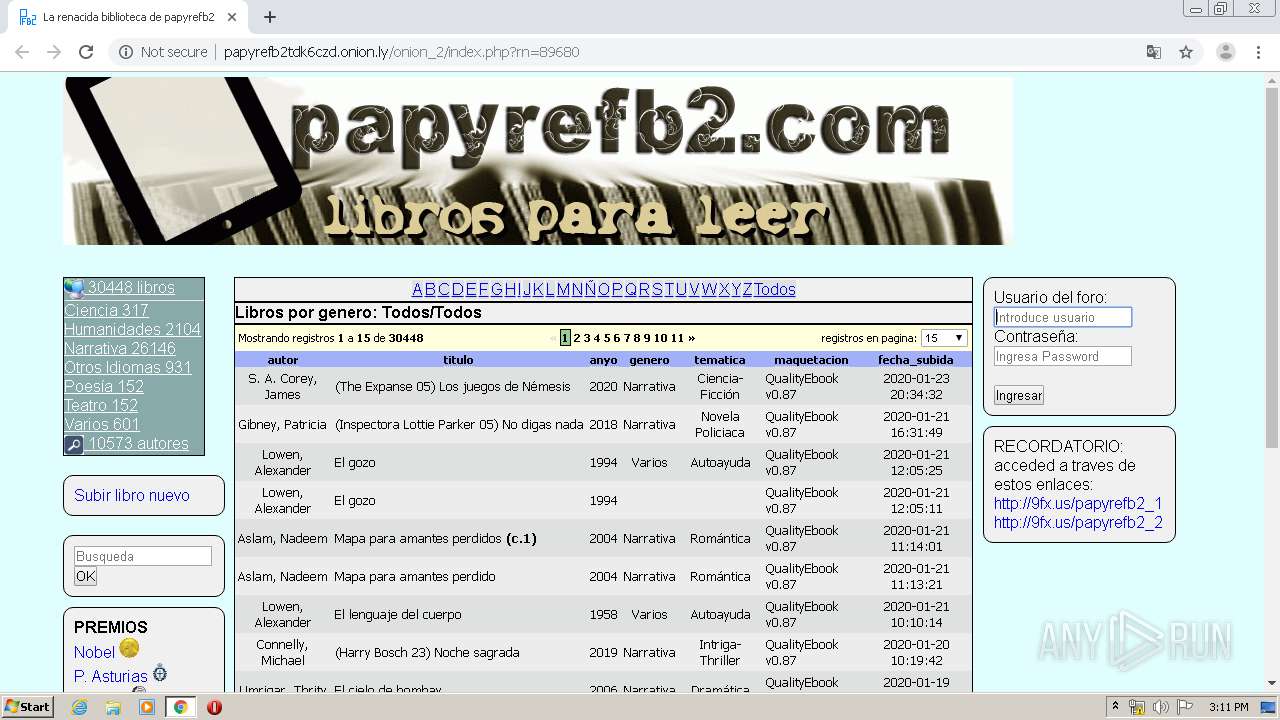
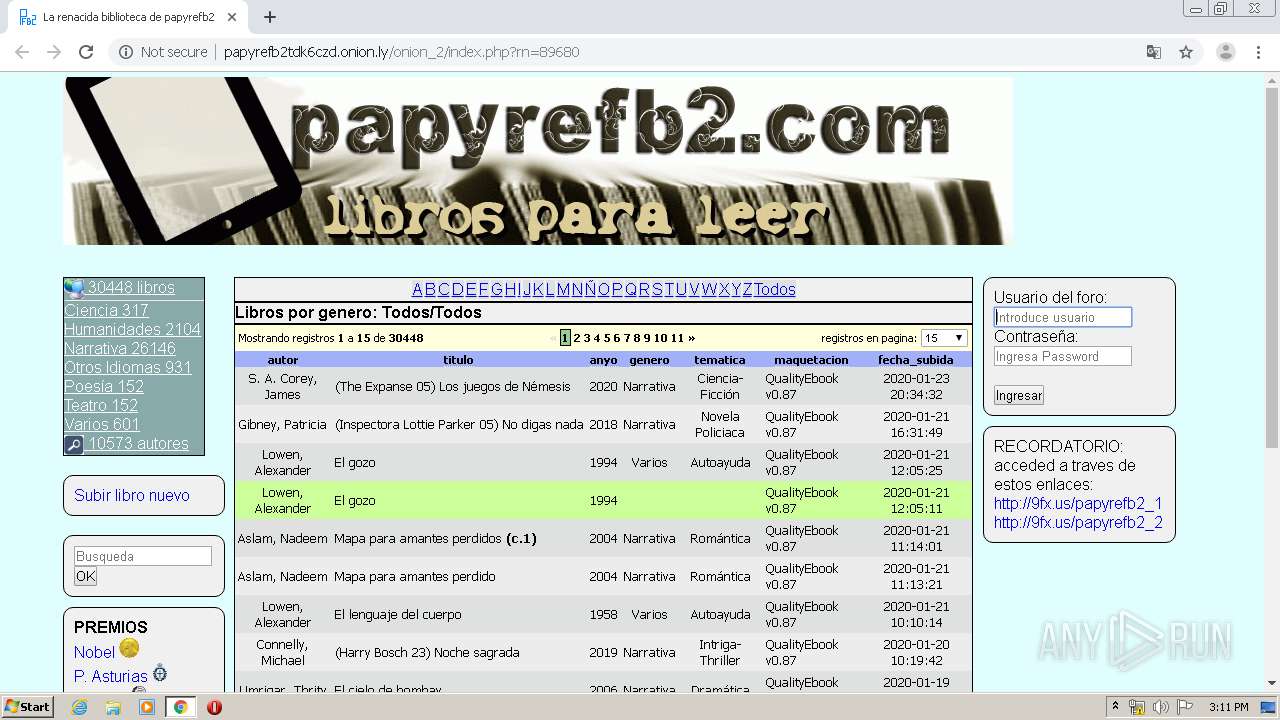
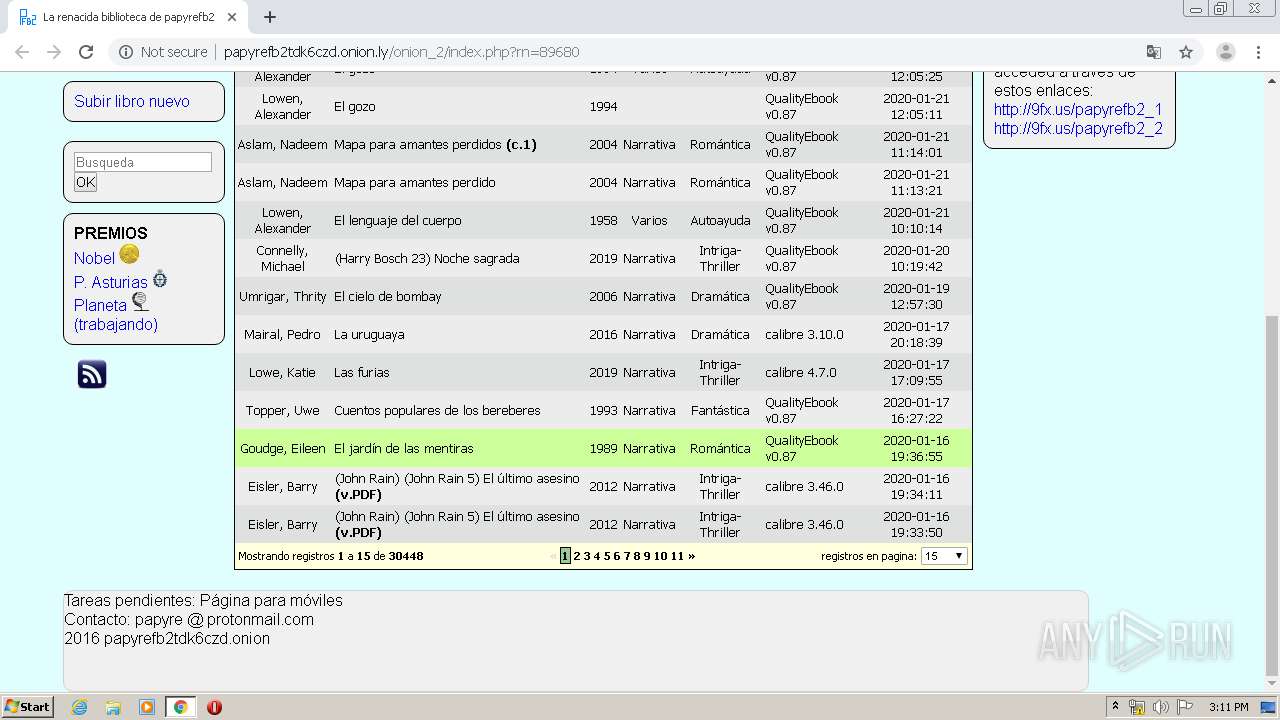
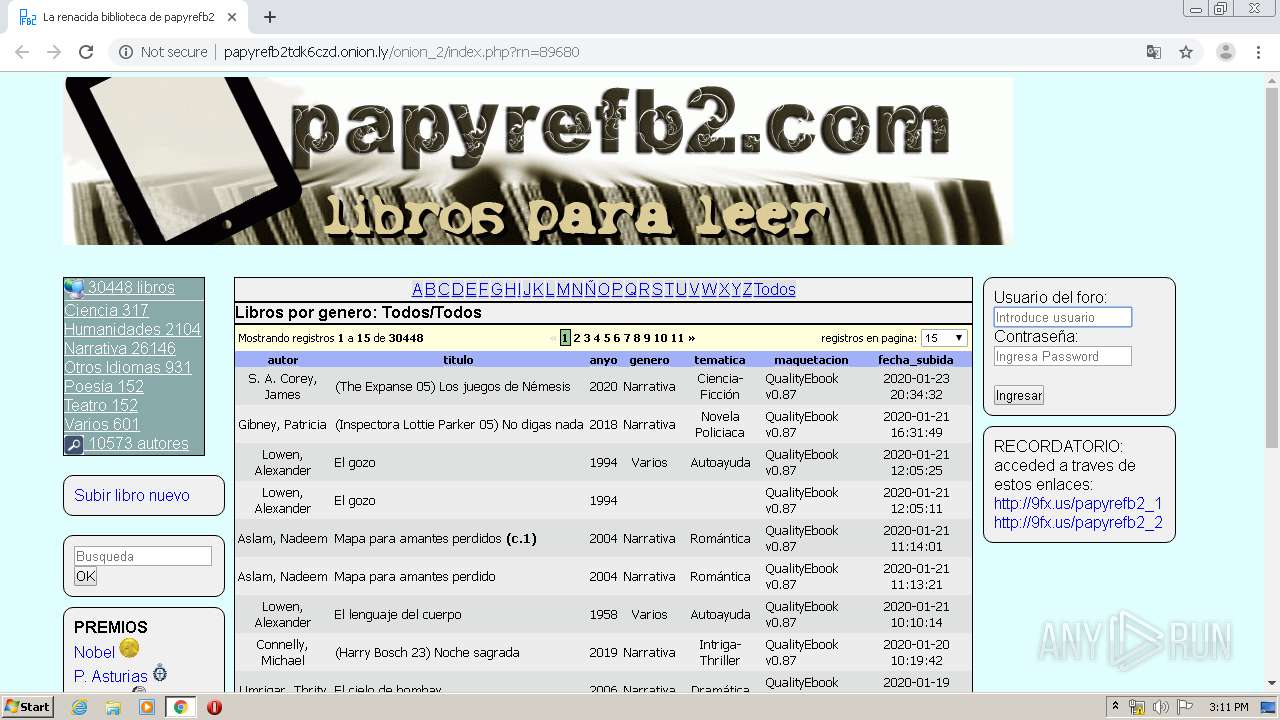
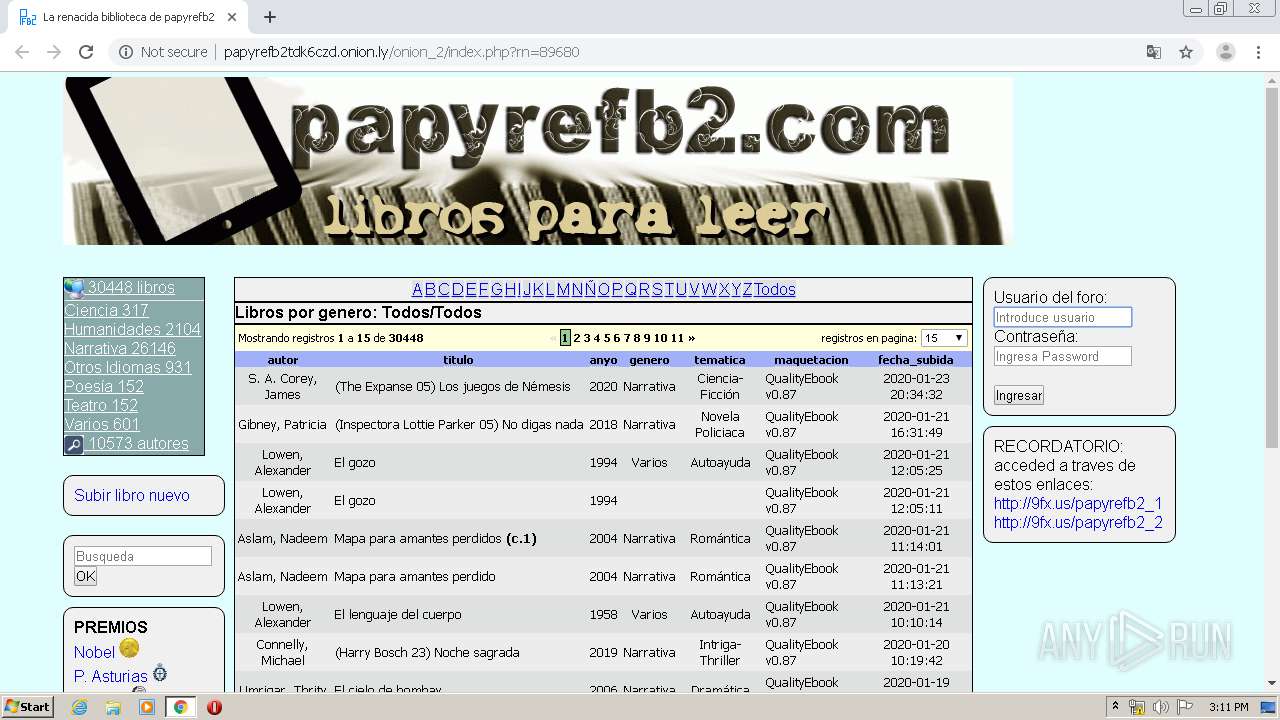
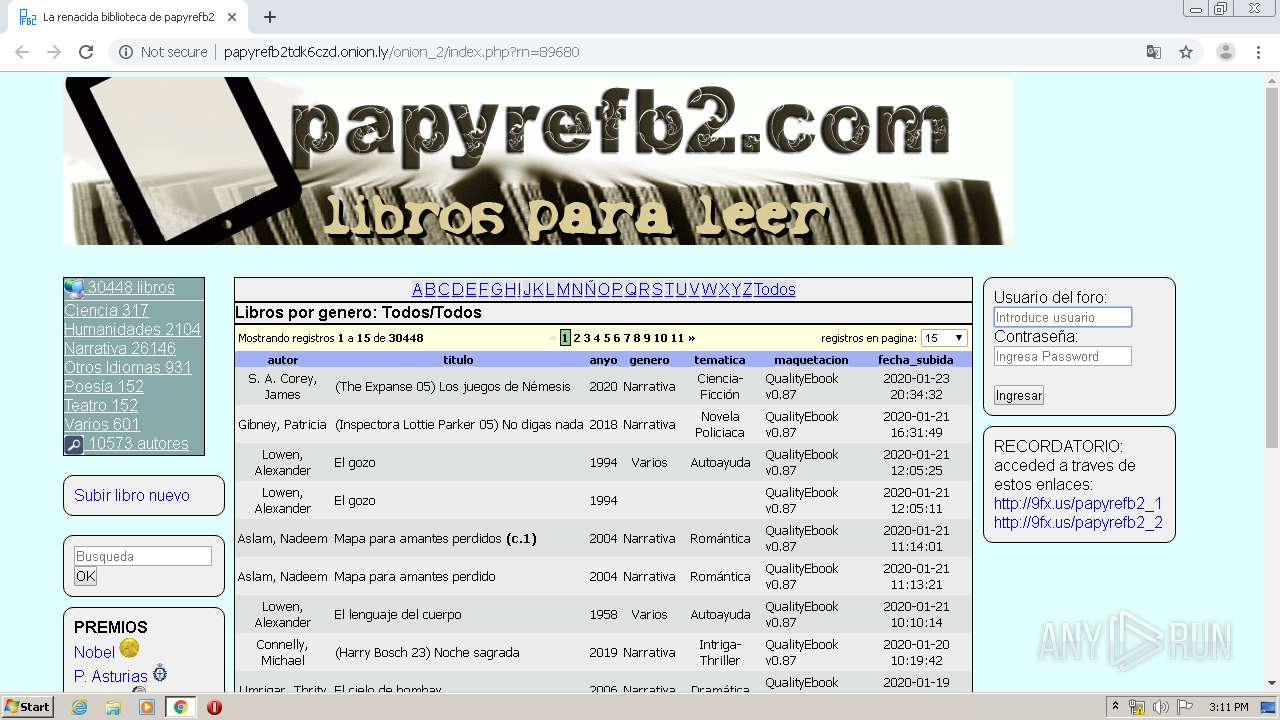
| URL: | http://papyrefb2tdk6czd.onion.ly |
| Full analysis: | https://app.any.run/tasks/ef2634b8-0b27-47b5-b942-af7141d8465b |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2020, 15:06:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6B229A4B151B8E17EA7F6F79FD5317A0 |
| SHA1: | 0E1395326F9AE7B0CDE8B887BED5AEB7BE3D6885 |
| SHA256: | 725C89B937C5CC23E37DE90EB24FC1F8B8121C174D6E4B5792D665146D1770BD |
| SSDEEP: | 3:N1KOEVcXwXRZf9KLL/S:COFAQHq |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2192)
INFO
Reads the hosts file
- chrome.exe (PID: 2192)
- chrome.exe (PID: 3840)
Application launched itself
- chrome.exe (PID: 2192)
Reads settings of System Certificates
- chrome.exe (PID: 3840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
29
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://papyrefb2tdk6czd.onion.ly" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa8a9d0,0x6fa8a9e0,0x6fa8a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=660 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 2956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,12215625952044961603,16437872658597225210,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6035605857383854973 --mojo-platform-channel-handle=956 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 75.0.3770.100 | ||||
| 3840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,12215625952044961603,16437872658597225210,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2096532292455488183 --mojo-platform-channel-handle=1536 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 2556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,12215625952044961603,16437872658597225210,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14649663980425564134 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 3300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,12215625952044961603,16437872658597225210,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10256855820569876288 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2288 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 3228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,12215625952044961603,16437872658597225210,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17208517300614370576 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2508 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 2852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,12215625952044961603,16437872658597225210,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10614750155092286629 --mojo-platform-channel-handle=3408 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,12215625952044961603,16437872658597225210,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=6946907585417795041 --mojo-platform-channel-handle=1044 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
Total events
685
Read events
601
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
16
Text files
266
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E2B0810-890.pma | — | |
MD5:— | SHA256:— | |||
| 2192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f2a36162-fc99-4ce6-82af-b073102a9426.tmp | — | |
MD5:— | SHA256:— | |||
| 2192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:33B05E8AC9C178C58ED3321F496588C0 | SHA256:2CDF6A09638A0B563EA2672D6926210771902E0A9203FE15D2857FC4EB954CDE | |||
| 2192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa66c01.TMP | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
| 2192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFa66c3f.TMP | text | |
MD5:AC43135B8C9FED46A92448C4E711F45C | SHA256:D840BA7CEBACF86DDBAD75BFB61A53449AA7AE3DE6B8ADC97FE45624626A6F09 | |||
| 2192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
| 2192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66c01.TMP | text | |
MD5:DA692BE42E4EF2668AE7499A7D5DA720 | SHA256:EB865CAF59002C092F5FDBE22D01935866BC1277108B29E897052CB2439630ED | |||
| 2192 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:DA692BE42E4EF2668AE7499A7D5DA720 | SHA256:EB865CAF59002C092F5FDBE22D01935866BC1277108B29E897052CB2439630ED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
40
DNS requests
69
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3840 | chrome.exe | GET | — | 198.251.89.118:80 | http://papyrefb2tdk6czd.onion.ly/ | US | — | — | malicious |
3840 | chrome.exe | GET | — | 198.251.89.118:80 | http://papyrefb2tdk6czd.onion.ly/ficha/includes/41112.jpg | US | — | — | malicious |
3840 | chrome.exe | GET | — | 198.251.89.118:80 | http://papyrefb2tdk6czd.onion.ly/ficha/includes/41110.jpg | US | — | — | malicious |
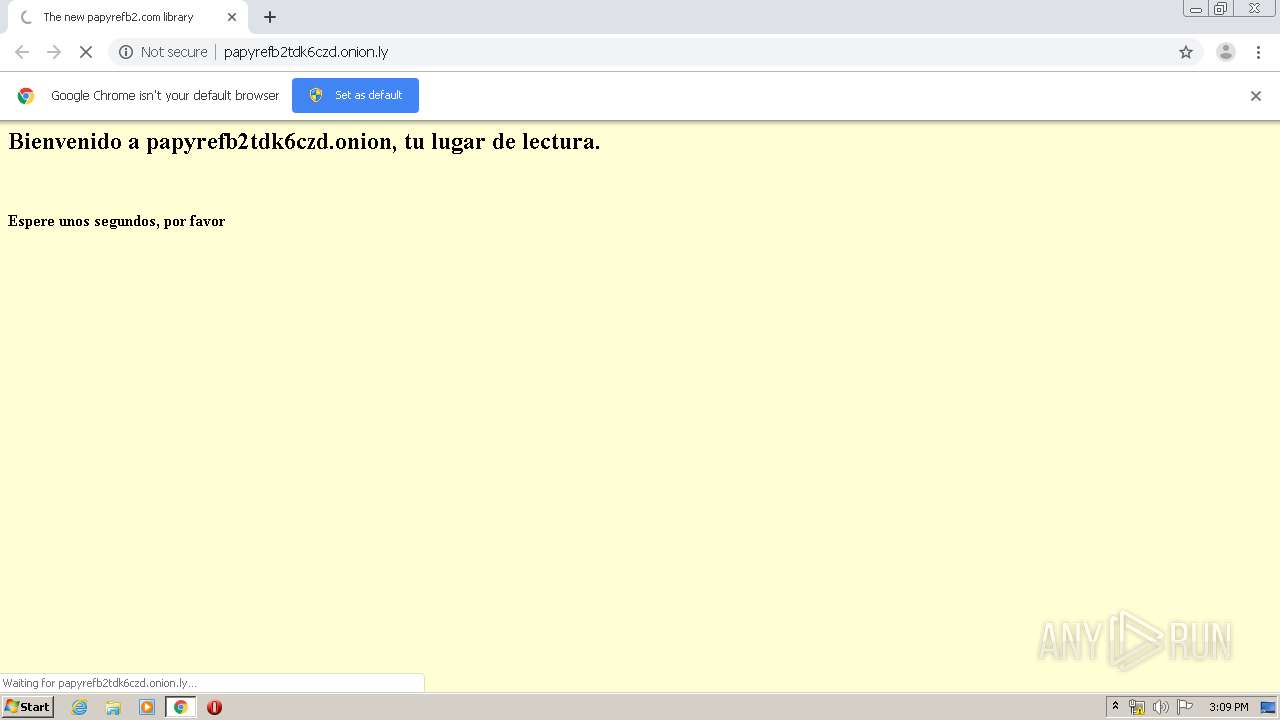
3840 | chrome.exe | GET | — | 198.251.89.118:80 | http://papyrefb2tdk6czd.onion.ly/onion_2/index.php?rn=89680 | US | — | — | malicious |
3840 | chrome.exe | GET | — | 198.251.89.118:80 | http://papyrefb2tdk6czd.onion.ly/onion_2/templates/default/style.css | US | — | — | malicious |
3840 | chrome.exe | GET | — | 198.251.89.118:80 | http://papyrefb2tdk6czd.onion.ly/ficha/includes/41109.jpg | US | — | — | malicious |
3840 | chrome.exe | GET | — | 198.251.89.118:80 | http://papyrefb2tdk6czd.onion.ly/onion_2/templates/default/style.css | US | — | — | malicious |
3840 | chrome.exe | GET | — | 198.251.89.118:80 | http://papyrefb2tdk6czd.onion.ly/onion_2/icons/search.gif | US | — | — | malicious |
3840 | chrome.exe | GET | — | 198.251.89.118:80 | http://papyrefb2tdk6czd.onion.ly/ficha/includes/41111.jpg | US | — | — | malicious |
3840 | chrome.exe | GET | 200 | 198.251.89.118:80 | http://papyrefb2tdk6czd.onion.ly/ | US | html | 1.82 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3840 | chrome.exe | 172.217.169.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 198.251.89.118:80 | papyrefb2tdk6czd.onion.ly | FranTech Solutions | US | malicious |
3840 | chrome.exe | 216.58.212.14:443 | clients4.google.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 172.217.169.206:443 | clients1.google.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 172.217.169.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 216.58.212.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 216.58.206.200:443 | www.googletagmanager.com | Google Inc. | US | unknown |
3840 | chrome.exe | 216.58.206.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 216.58.206.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 209.85.226.106:80 | r5---sn-5hne6ns6.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
papyrefb2tdk6czd.onion.ly |
| malicious |
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
dns.msftncsi.com |
| shared |
www.gstatic.com |
| whitelisted |
clients4.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3840 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM TIMEWAIT ACK with wrong seq |
3840 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM TIMEWAIT ACK with wrong seq |
3840 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM TIMEWAIT ACK with wrong seq |
3840 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM TIMEWAIT ACK with wrong seq |